
hot-takes
Raspberry Pi as a security device, pipe dream or reality?
An exploration into the question: could you use a Raspberry Pi to improve network security for a small business? Haters will say...

comedy
Ignorance is a flimsy shield.

If you've been around the internet for as long as I have, you might have come across the incredibly annoying, and, quite frankly, weird phenomenon that is people not knowing their own email address. You see, one of my email accounts is a Gmail account that I got

hot-takes
The Company continues to profit from hate.

hot-takes
The US election wasn't free. It cost a pretty penny, but how much did the Company gain?

howto
Resources & references on where to report phishing attempts

our daily breach
Internet Archives is under attack... again. Hackers love this single trick to maintain persistence.

howto
Building a cybersecurity program from the ground up is hard. This series of articles will present ways of establishing your cybersecurity program the right way.

our daily breach
I didn't want to write this post. I was Space Forced to.

our daily breach
FBI hacker 'USDoD' struggles with his own data breach. I mean... it's kind of funny.
Cybersecurity Truths

Bad dog! No hacking the SEC!

Fidelity rewards customer loyalty by sharing the private identities of 77,000 customers. American Income Life Insurance is being extorted.

Welcome back to another thrilling day of infosec management. Today we are going to take everything we learned in part 1 and turn it into a fearsome tool you can use to impress your friends, motivate your team, and banish your auditors back to their dark domain. I'm
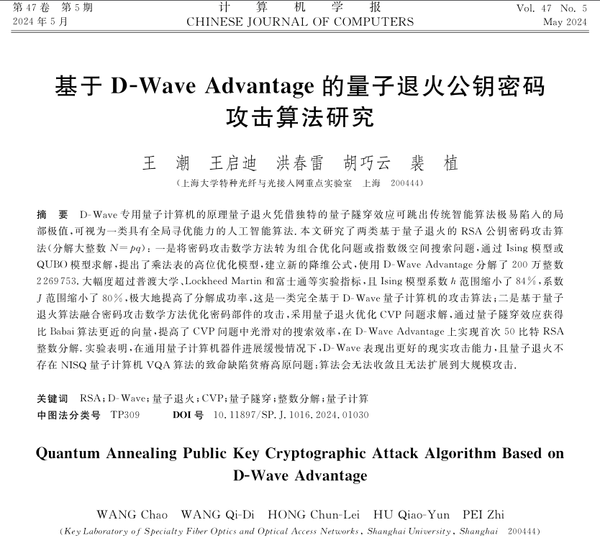
Chinese researchers weaken RSA encryption with quantum computing.

First rule of Casio club is you don't talk about data breaches. The second rule of Casio club...

Back in the day, I was a pretty avid Google Reader user. For those of you too young to remember it, Google Reader was a very cool thing: it was an RSS reader, but it was also a social reader because people could follow you and see what kind of
It's a happy Canadian Thanksgiving for everyone except the libraries of Calgary.
The Internet Archive gets DDoS'd and breached by hacktivist group. The rage is palpable.

Gasp! Comcast lied about the impact of its data breach.

ADT files 8-K disclosing a breach of employee data. The company goes on a journey believing that no client is impacted.

Credit Monitoring firm CreditRiskMonitor gets breached. Quis custodiet ipsos custodes?

Depending on who you ask, bouncing back from ransomware attacks will cost organizations anywhere from 5 to 20 million US dollars. That's not loose change, but that's nothing that will make a dent on the bottom line of a significant number of organizations. If you do